Tag: security
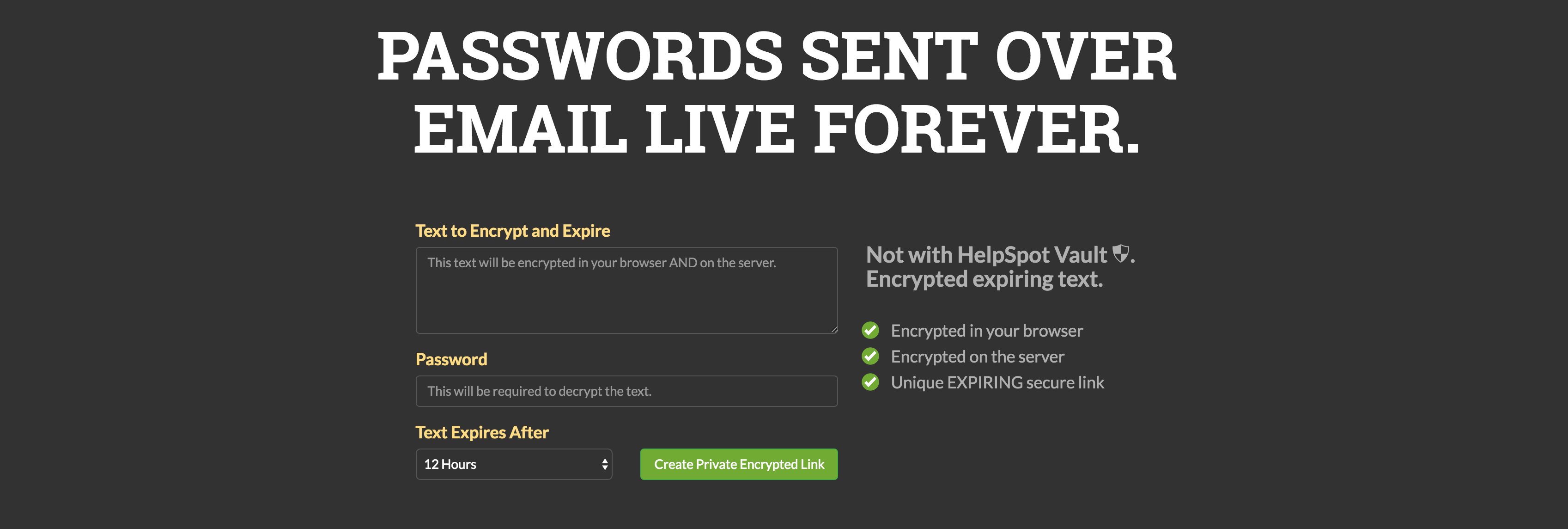
Next time you need to send someone something like an account login or a password, OneShar.es lets you do this in a secure fashion. Paste your data into…
rpg is a command line tool that helps you create random password which you can use for any purpose. ~ sepisoad/rpg
If you’re using the InfiniteWP WordPress Client plugin to manage your website, now is a good time to update. While doing a routine audit of our Website Firewall…
This article a great reminder as to why you should always keep your WordPress install updated with the latest version. If you’re running the latest version of WordPress…